Unfortunately many people think that just using a VPN is enough by itself is enough to protect their privacy and security online.
Of course using a VPN is very important if you are concerned about privacy and security, but it’s not the only measure you should take. Here are some additional tips.
1. Choose your VPN provider carefully
Your online privacy and security is only protected to the extent that you trust your VPN provider. Just because they write on their website that they don’t log your activity that doesn’t mean they are telling the truth. When choosing which VPN provider to use you should look into the company behind the VPN. What are the logging policies? How will they use your personal data? What country are they based in and what laws do they need to comply with? Do a search on Twitter or Reddit and see if there are unresolved customer complaints. Make sure you trust the company you are dealing with. Personally I consider all of the VPN providers listed on this website to be trustworthy.
2. Check for WebRTC leaks
You may think that by connecting to a VPN that your real IP address and location is hidden. This is not always the case. If you are using Chrome or Firefox then you might be at risk of leaking your real IP address and location. You can check if you are affected by following these steps.
– Check your real IP address by visiting this page without a VPN connected.
– Check your VPN IP address by visiting this page with your VPN connected.
– With your VPN still connected open this page and see if your real IP address is shown.
If you see your real IP address then you are affected by the WebRTC leak. If this simple website with a few lines of code can so easily discover your real IP and location then how difficult do you think it is for other websites you visit to get this information?
The best way to stop this leak and protect yourself against future vulnerabilities is to run your VPN on your router instead of your computer. With the VPN off your computer there is no way to bypass it.
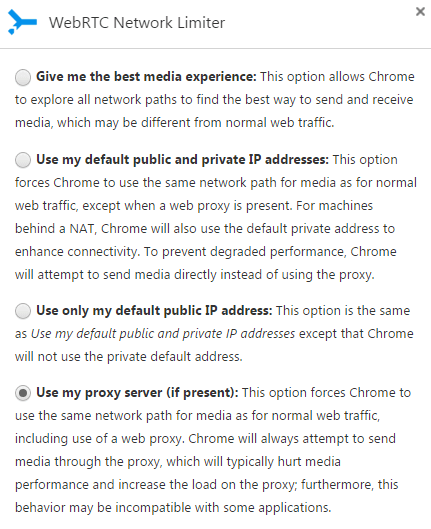
Another way to stop the WebRTC leaks on Chrome is to install the WebRTC Network Limiter extension. My Windows 7 computer was affected by this leak and I stopped it by using the WebRTC Network Limiter extension with the “Use my proxy server (if present)” option selected as shown below.
For Firefox you can open about:config in your address bar and then set media.peerconnection.enabled to false.
3. Check for DNS leaks
DNS leaks happen when your operating systems doesn’t properly assign the DNS servers from your VPN. Your DNS queries then go through your ISP DNS instead of the VPN. If you are in China or other country that censors the internet and you can’t load blocked sites even after connecting to a VPN then you most likely have a DNS leak.
You can check for DNS leaks by running an extended test on this page. If you are connected to a VPN and you see your ISP DNS servers here then you have a leak. Most leaks can be fixed by manually assigning public DNS servers on your network adapter. You can find a list of public DNS servers here. If you are outside China then Google is recommended. If you are in China you can try Norton, Level 3, or 114.114.114.114 and 114.114.115.115 which is a very good Chinese public DNS. Never use your ISP’s DNS even if you are not using a VPN.
4. Block ads and tracking scripts
There are many good browser extensions to block ads and tracking scripts. I recommend Adblock Plus to block unwanted ads and Disconnect to block tracking requests.
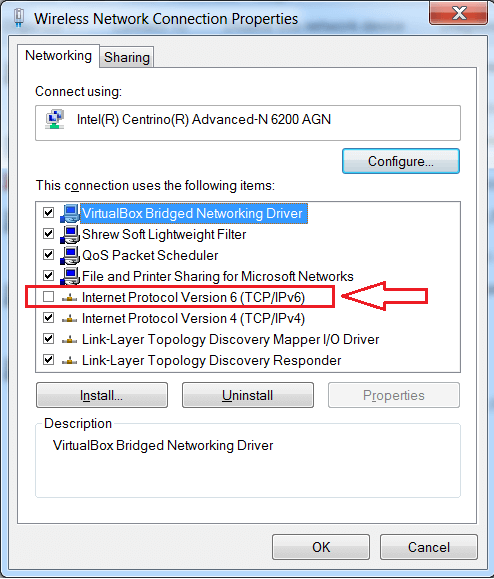
5. Disable IPv6
IPv6 is insecure and should be disabled if you don’t need it. If you don’t know what IPv6 is or don’t know whether you need it then just disable it first and see if there is any effect. To disable IPv6 simply uncheck the item called Internet Protocol Version 6 (TCP/IPv6) in the properties of your network adapter. Follow the same instructions as changing your DNS server to find the network adapter properties.
6. Download android apps from the Play Store only
If you are using an Android phone try not to download any apk files outside of the Play Store. If you are in China that means you must use a VPN. The apps in the Play Store have passed checks by Google and are much less likely to contain malware, spyware, and viruses.
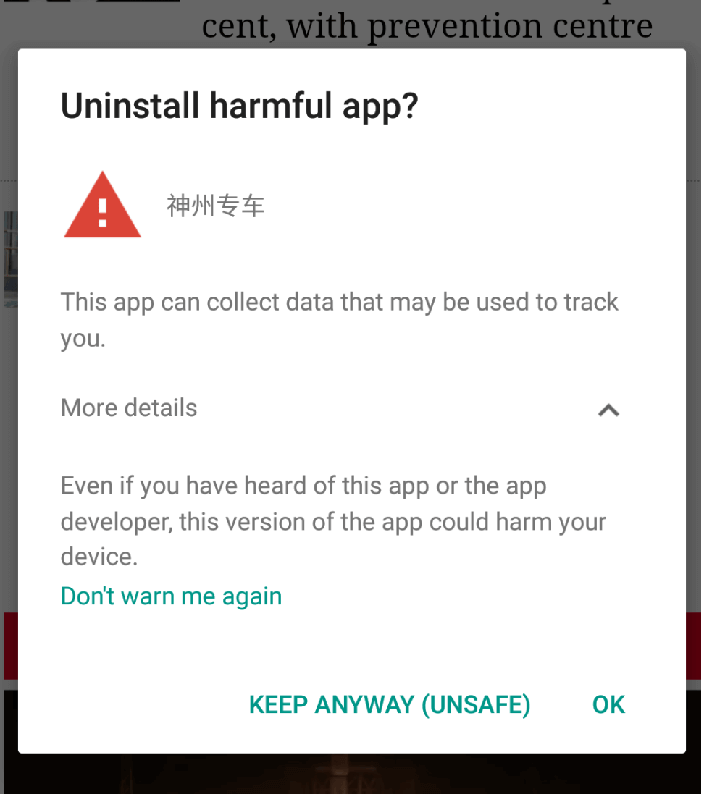
If you must download certain apps not available in the Play Store then it’s recommended to change the permission settings for that app. Disable any permissions that you don’t think are necessary for that app. Furthermore if your phone is rooted you can freeze these apps when you are not using them. I had to do this recently with a Chinese Uber-like app called U-car (神州专车). Originally I download the app from the Play Store but recently when I opened the app I was told there was a mandatory update. Only two options – update or exit.
I rejected the in-app update and checked the Play Store for an update only to find this app was removed from the Play Store completely. I had to download the apk because I have a balance over 3,000 yuan. Otherwise I would have just stopped using it. Now I keep it frozen with Titanium Backup (pro version) and unfreeze it when I need use it. I often get the below message on my phone. Now I understand why it’s not in the Play Store anymore.
7. Use WhatsApp instead of WeChat
This is a special tip if you are in China. If you are not in China then you are probably already using WhatsApp and don’t even know what WeChat is.
WhatsApp is fully encrypted on both ends. Not even WhatsApp can decrypt your conversions stored on their own servers. If they are asked to do so by government agencies or others they are simply unable to comply with the request. WeChat on the other hand…. Sure WeChat is popular in China but for sensitive conversions WhatsApp is a much better choice. Actually it’s surprising that WhatsApp has not already been blocked in China.
Other tips
Do you have any more tips to add to this list? Please leave your comments below.